
Adobe Flash Player Now Sandboxed in Safari on OS X Mavericks
Adobe announced that it's Flash Player will now be sandboxed for it's Safari version found on OSX Mavericks. Preventing malware targeting Flash from accessing sensitive data and system resources.

Headline: Google Two-Factor Authentication Compromised
Duo Security figured out how to bypass Google's two-factor authentication, abusing Google's application-specific passwords. Curiously, this means that application-specific passwords are actually more powerful than users' regular passwords, as they can be used to disable the second factor entirely to gain control of an account.

Review: iTwin Connect
iTwin Connect ensures that no one can eavesdrop upon your activities when you access the Internet from untrusted networks. Plug in one half of your iTwin and select the "Teleport Me" feature. iTwin Connect encrypts all your data and routes it through the host server of your choice. It can be either one of the iTwin dedicated servers set up in various locations for your convenience or it can be a Trusted PC to which you have attached the other half of your device.

VPN: OpenVPN installation and config
Join us as we install one of the most secure VPN services "OpenVPN".

VPN: L2TP Server installation and config
Need help tackling L2TPwe got your back. It's one of the more trickier VPNs to configure and setup. It's encryption is stronger then PPTP and is widely available with out 3rd party software and supports most Mobile devices makes this a top choose for tunneling though the internet

Headline: Oracle Java 7 plug-in blocked by Safari in the wake of a zero-day exploit
Apple has blocked Safari on Macs from running Oracle’s Java 7 in the wake of a zero-day exploit for Java:

VPN: PPTP Server installation and config
While not the most secure of the VPN solutions out there, PPTP is by far the simplest to get up and running. Join us as we install PPTP on a Debian distro.
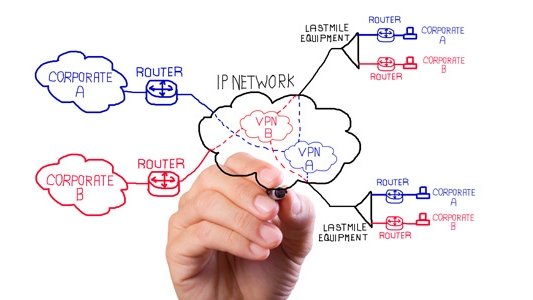
VPN Protocols: Introduction and Security
Protecting your personal information is not the only concern one should have. Their are many other threats out their like viruses, malwares, trojans, spam etc, which will infiltrate your computer system if you are not careful. There are also dishonest people who hack and phish your information when your online. Protecting your online identity is so important that it becomes a job of its own.

Security: Secure Your LastPass Account Even More
Locking down your Lastpass account and protecting your valuable data.

Security: two factor authentication - YubiKey
Google's Hangouts On Air is there way for musicians to stream concerts from their garage or the stadium, so today it launches Studio Mode, an option that lets broadcasters optimize sound quality for real-time music instead of voice.
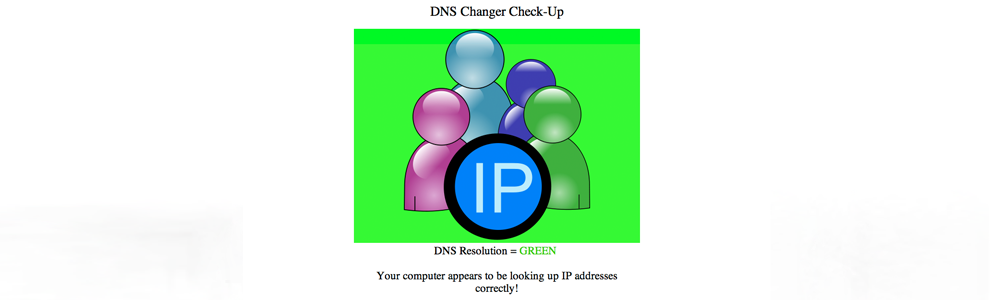
Security: Will Your Internet Work on Monday? Check for DNS Malware
The FBI is shutting down domains that have been affected by the DNSChanger malware. This malware redirect's Internet traffic to sites with paid advertisements where cyber criminals profit from unsuspecting visitors. Creators of this trojan where shut down when they were caught and arrested about eight months ago.

Headlines: NXP Smart gesture cards
With the rapidly expanding growth of Near-Field Communication (NFC), concerns about security and privacy are growing along with it.

Apple to Issue Update to Remove "MacDefender" Malware
Apple has posted a Knowledge Base article that addresses the recent MacDefender malware issue and also stated they will be addressing it with in the next few days with a software update. Apple describes "MacDefender" as a recent phishing scam that has targeted Mac users by redirecting them from legitimate websites to fake sites which tell them that their computer is infected with a virus. The user is then offered Mac Defender "anti-virus" software to solve the issue.

Guide: iOS Parental Control Setup
One of the most asked questions for iOS devices is. How do I control what my kids can do on their iOS device? Thankfully Apple has incorporated some nice parental controls into their OS. We are going to dive right in with a step-by-step guide on configuring these parental control options in iOS

Facebook: HTTPS Support
Those who are concerned about online security probably know that it was possible to access Facebook via HTTPS for quite some time now, for example using the HTTPS Everywhere Firefox add-on, but some of Facebook’s features, for example chat and photo uploads, did not work properly over HTTPS.
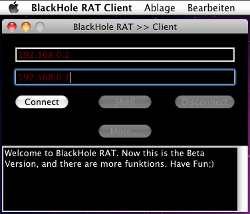
WARNING: NEW-Mac OS X backdoor Trojan
Sophos one of the leading Antivirus software company's have found a new backdoor trojan targeting Mac OSX users. It seems it is a variant of a well-known remote access trojan (RAT) for windows users known as darkComet or BlackHole. However Sophos calles it OSX/MusMinim-A or MusMinim for short. .
LastPass Acquires Xmarks!
Xmark has been acquired by LastPass Makers of the leading cross-platform password manager

Mac app store hacked, how developers can better protect themselves « Craftymind
Mac app store hacked, how developers can better protect themselves Crude instructions have started showing up online with ways to circumvent Apples Mac App store receipt validation. By simply copying receipt and info.plist data from a free app and pasting it into a paid app, you can run apps copied from friends computers or bittorrent. I myself have a copy of a paid app (not angry birds, but one with stronger protection) running on my system that was purchased by a friend. This is a massive failure in the implementation of Apples receipt system.
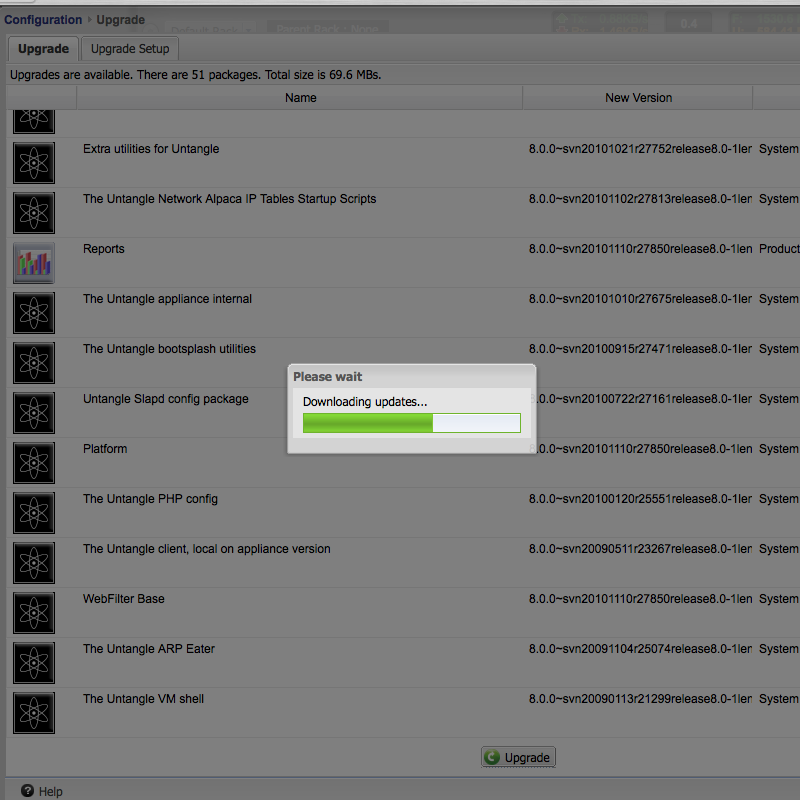
Untangle - Upgrade
Untangle Upgrade to v8 went off with out a hitch very smooth no issues at all. All my racks settings (dhcp, certificate, port forwarding, QOS etc...) were still in place.

